Simple fix for CSP: Inline Scripts Can Be Inserted
Abstract:
After conducting a thorough pentest on our web application, we discovered vulnerabilities in our Content Security Policy (CSP) related to inline scripts. This article discusses how we implemented the Nonce CSP directive to mitigate these vulnerabilities and enhance the security of our application.
Introduction:
Content Security Policy (CSP) is a crucial security mechanism that helps protect web applications against various types of attacks, including cross-site scripting (XSS) attacks. However, CSP configurations need to be carefully crafted to balance security and functionality. One common challenge is dealing with inline scripts, which can bypass CSP restrictions if not properly controlled.
Understanding the Issue:
During the pentesting process, we identified that our CSP configuration allowed the use of 'unsafe-inline' and 'unsafe-eval' directives for script execution. While this provided flexibility in terms of development, it also introduced significant security risks. Attackers could potentially inject malicious scripts via inline script tags or event handlers, compromising the integrity of our application.
Implementing Nonce CSP:
To address this issue, we decided to implement the Nonce CSP directive. Nonce (number used once) is a cryptographic value that serves as a unique identifier for inline scripts. By generating a random nonce value for each inline script and including it in the CSP header, we can ensure that only scripts with matching nonces are executed.
Here's how we implemented Nonce CSP:
-
Generating Nonce Values:
- We modified our server-side code to generate a unique nonce value for each HTTP response.
- Nonce values are securely generated using cryptographic functions to prevent predictability.
-
Including Nonces in CSP Header:
- We updated our CSP header to include the 'nonce' attribute along with the generated nonce value.
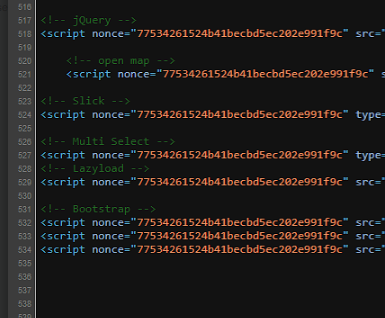
- Inline script tags in our HTML documents are modified to include the 'nonce' attribute with the corresponding nonce value.
-
Enforcing CSP Policy:
- With the Nonce CSP directive in place, the browser will only execute inline scripts that include the correct nonce value.
- Any attempt to inject inline scripts without the correct nonce will be blocked by the browser, mitigating the risk of XSS attacks.
-
Testing and Validation:
Benefits and Impact:
Implementing Nonce CSP for inline scripts has several benefits:
- Enhanced Security: Nonce-based CSP prevents unauthorized execution of inline scripts, reducing the risk of XSS attacks.
- Improved Compliance: By adhering to best practices for web security, we demonstrate our commitment to safeguarding user data and privacy.
- Minimal Impact on Functionality: Despite tightening our CSP policy, the impact on application functionality is minimal, thanks to careful testing and implementation.
Conclusion:
Implementing Nonce CSP for inline scripts has significantly strengthened the security posture of our web application. By addressing the vulnerabilities identified during the pentesting process, we demonstrate our dedication to proactive security measures and protecting our clients from potential threats. We encourage other organizations to consider implementing similar measures to enhance the security of their web applications.
References:
- Content Security Policy Level 3 - W3C Recommendation: https://www.w3.org/TR/CSP3/
- OWASP Content Security Policy Cheat Sheet: https://cheatsheetseries.owasp.org/cheatsheets/Content_Security_Policy_Cheat_Sheet.html
- Google Developers - Web Fundamentals: https://developers.google.com/web/fundamentals/security/csp
- https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/script-src
- https://content-security-policy.com/unsafe-inline/
- https://content-security-policy.com/nonce/
- https://content-security-policy.com/hash/
Bogdan Iacob, 28th March 2024